What is Incident Management?
The difference plays out in remediation and how responders approach fixing the issue. The other Service Owner provides services that support delivery of IT services to Service Owner A’s customers. This is how blameless postmortem helps to spread the necessary information and the discovery of the root causes of incidents. Stay in control with real time operational intelligence. Finally, we’ll examine how new integrated service management software facilitates automation and helps organizations establish a consolidated service desk and resolve incidents more efficiently. Even with preventative measures like data log security monitors and firewalls in place, various system issues like memory, capacity, or sophisticated cyber threats might slip under your radar. In order to provide all necessary information, a system for managing incidents needs to have functionalities that allow categorization, linking, and tracking of issues. Roles and Responsibilities. You forgot to provide an Email Address. Incident management is the process of managing IT service disruptions and restoring services within agreed service level agreements SLAs. Class is typically held from 0800 1700 hours with a one hour lunch from 1200 1300 hours. Root cause analysis tools help IT staff understand how a system operates and where any incidents reside. Map the scope of impact across affected systems, business processes, operating jurisdictions, and regulatory authorities. The second is a manual report. Automation is a great way to put a unified process in place to meet the service demands of employees. Select an Impacted service – this will alert the response team. Set salary expectations upfront. The Incident Management team is comprised of the following. This way, you can fix the underlying problem once and for all. It does so by guiding and advising EU Member States on how to set up and operate a CSIRT or Security Operational Centre SOC as well as by increasing cross border collaboration and enhance and improve incident response capabilities and readiness across the Union through EU CSIRTs Network. Call now 0508 664 981. As an Incident Commander, you have to lead a team of responders. In spite of your DevOps team’s best efforts, there is always a possibility for incidents to occur. It’s a low code platform that allows for the creation of custom forms. Thanks for your reply,. This type of network inventory software is useful for incident management because it provides in depth details about any errors or disruptions within the program.

All Services
Alert management helps set up alerts and monitor anomalies in time series metrics over a certain period. Finding, retaining, and inspiring a high performing staff that is in accordance with the aims and objectives of the firm is the aim of human resource management. You can even apply fully customizable filtered views to decide which incidents you wish to see and work on. Incident Prioritization Guideline. In the first place, the incident manager will create a Major Incident Management Team with the best engineers to analyze the incident. If incidents of any type or severity are slowing you down, or your team spends too much time acknowledging and assembling vs. The following diagram is an example of Dependency Views. Each course includes content of traditional in person classroom training via Zoom technology. And are handled with a predefined request fulfillment process, instead of with your incident management process. Some of the most commonly used incident management tools include. Purchasing and licensing. I review and initiate any policy changes the Secretary determines necessary and appropriate to clarify and modernize immigration pathways for experts in AI and other critical and emerging technologies, including O 1A and EB 1 noncitizens of extraordinary ability; EB 2 advanced degree holders and noncitizens of exceptional ability; and startup founders in AI and other critical and emerging technologies using the International Entrepreneur Rule; and. This is to prevent a future re occurrence of hazards. This means encouraging and facilitating ongoing communication, collaboration, and learning among personnel, as well as providing them with access to resources and services that can enhance their physical, mental, and emotional health. Incident management is the process used by development and IT Operations teams to respond to an unplanned event or service interruption and restore the service to its operational state. The service desk employee tries to quickly diagnose the problem on a surface level so that it can be redirected to the relevant team. Incident management platform what is it. The customer must verify the resolution within a specified time period, or Incident Management automatically moves the incident request status to Closed.

Critical Incident Stress Management
CISM is based on several principles, such as respect, confidentiality, flexibility, and cultural sensitivity. Major Incident Manager conducts functional or hierarchic escalation based upon the Escalation Schedule defined earlier and updates the https://postincidentreviews.com/incident-management-secrets/ incident record. Major incidents can cause major damage to an organization’s reputation and can affect the overall business. The business/organisation’s policy is to have an effective and efficient system for responding to major incidents, which is appropriate to the individual circumstances. Additionally, advancements in scanning technologies allow attackers to scan the entire internet quickly and easily to locate attack vectors, revealing abandoned, rogue, or misconfigured assets that can become backdoors for compromise. SolarWinds Service Desk is an incident management solution that empowers teams with automated processes. We further create Change Requests based on the given situation. E To improve transparency for agencies’ use of AI, the Director of OMB shall, on an annual basis, issue instructions to agencies for the collection, reporting, and publication of agency AI use cases, pursuant to section 7225a of the Advancing American AI Act. Domotz and ServiceNow create a streamlined journey for solving issues with the networks and devices you are monitoring and managing. One of our training consultants will get in touch with you shortly.
Sprinto: Your growth superpower
ITSM’s key concept is that IT should be delivered as a service, and incident management is one of its practices. Work can be at incident camps, on site, school rooms, and office settings. After all, without the right people to support them and put them into practice, security policies, processes and tools mean very little. Analyzing this metadata helps identify the hot spots in the operational aspect of the organization. Boundary value analysis provides multiple benefits, including increased test coverage and proactive defect prevention. The spring tide, the loading difficulties at Zeebrugge harbour, etc. Otherwise, the same incidents will continue to recur, we’re still reliant on individual heroes to fix things, no root cause analysis gets done, so nothing gets fixed permanently, and opportunities for continual improvement are missed. Remember, embracing these action points is not just about damage control. I’ve always been interested in media, I’m qualified at level 3 film production. An incident is considered resolved when the technician has come up with a temporary workaround or a permanent solution for the issue. Anniston, Alabama $69,646 to $90,537 PA Apply by: Thu, 12/28/2023. Continuing Education Information:Two Day Course: 8:30 a.
Why choose IT Governance for cyber security incident management?
One of our training consultants will get in touch with you shortly. In fact, teams are spending 30% more time on duplicate work. Incident Logging and Categorization. These 12 tools approach patching from different perspectives. The incident comes from the users in whatever form the enterprise allows. JupiterOne aggregates and normalizes data from hundreds of different sources so you can identify and triage security risks easily. With on call management and 24/7 implementation support, PagerDuty empowers teams to have hassle free incident operations. Economy/Saver Shipping 5 20 Days. Copyright 2016 2023, TechTargetPrivacy Policy Cookie Preferences Cookie Preferences Do Not Sell or Share My Personal Information. Get bi weekly insights straight to your inbox. But, in practice, you can use our ready made, fully detailed process diagram, which can via the process editor generate documentation instantly. Regular updates on incident progress ensure effective communication, reduce unnecessary inquiries, and maintain transparency throughout the incident resolution process. These processes are closely coordinated with the service desk, which is usually the chief point of contact. This allows the developers to harden IPFire better than any other server operating system and build all components specifically for use as a firewall. It does so by guiding and advising EU Member States on how to set up and operate a CSIRT or Security Operational Centre SOC as well as by increasing cross border collaboration and enhance and improve incident response capabilities and readiness across the Union through EU CSIRTs Network. Determine stakeholders for communication. And talking about major incident communications, here some dedicated hints. The service desk employees should ideally check with the person who reported the incident to confirm that the resolution is satisfactory before actually closing the incident.

View all your data and tools in one place
Well designed metrics serve both as an indicator of progress for management and as a clear prescription for action by front line IT staff. “Yes it’s a coup but I disagree with you calling it that” my interpretation of Sutskever’s words. Lucidchart helps IT support professionals collaborate across the ITSM lifecycle, from incident management and beyond. This memorandum serves as public notice that the NIMS Guide 0005: Preparedness and Incident Management Standards, dated January 10, 2008, that provided an overview of the standards that support NIMS implementation will not be updated and archived. When system errors prevent network functionality, your employees will be uneasy about the privacy and quality of their work environment. Activities in an EOC include managing and providing information and resources, long term planning and other forms of coordination. As employees try to get to work the next day, they are stuck waiting for the login issue to get resolved. If something breaks, incident management is the process of restoring normal service operations as quickly as possible. Each of these will be helpful for references later on, especially if you have a problem management plan in place. A developing a companion resource to the AI Risk Management Framework, NIST AI 100 1, for generative AI;. A person who consumes the IT service on a day to day basis. These incidents can range from IT issues, such as system failures or cyber attacks, to physical emergencies, like workplace accidents or natural disasters. The subject matter expertise gained in an incident manager position creates some of a company’s most valuable IT employees. Incident categorization also helps the service desk system apply the most appropriate SLAs to incidents and communicate those priorities to end users. Technical incidents, on the other hand, are often identified during routine monitoring. Best with a self service chatbot. Even though Splunk on call formerly VictorOps is officially part of the Splunk ecosystem, the integrations to their monitoring are still not one click away, but are instead treated as regular integrations.
Follow us on
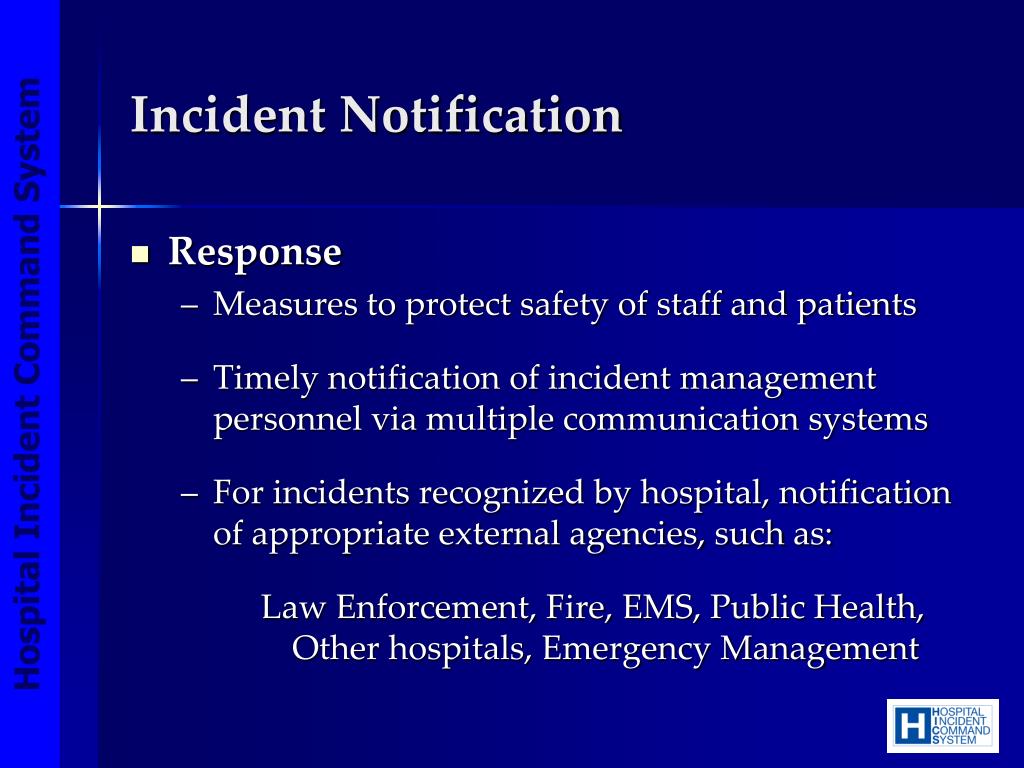
Major Incident Manager. This is done with the help of a five step process that ensures incidents get solved efficiently and correctly. Explore the pros and cons of different approaches to on call management. I figured this idea might be of use. Note: ‘informed’ means those who are kept up to date on progress, generally characterized by one way communication such as presentations. During a security breach or a natural disaster, some locations or processes may be inaccessible. He needed to set up a configuration item reference field or catalog variable that would display a calendar macro that, when clicked, would open a popup window containing a change calendar report for that configuration item. Just click here to suggest edits. In order to handle incidents in a way that meets the needs of customers and relevant stakeholders, your IT team will perform a variety of activities, generally in this order. An incident model helps service desks investigate, record, and resolve service interruptions or outages. Understanding their various approaches can help you find the right. This process is initiated when a user reports some malfunction to your company’s IT resource. It can help you prioritize alerts, uncover new threats, and accelerate investigations. Why I picked Freshservice: I picked Freshservice because it allows you to offer support via multiple channels like mobile apps, phone calls, feedback widgets, self service platforms, email, Freddy chatbot, and even walk ups. Annual Revenue: Approx. In fact, according to research by Gartner, major incidents emergency level service outages cost businesses up to $300,000 per hour. Incidents are registered on task cards, which show priority, tags, due dates and can be assigned to teams. These plans inform security members, stakeholders, authorities, legal counsel, and eventually users of the incident and what steps need to be taken. If everything has a similar look or uses a standard template, the brain can absorb the information better and quickly. As always, if you have any questions or comments regarding this piece or the OpsMatters platform, please leave a comment below or reach out to us at. Incident management helps to ensure your business has the IT support it needs to function efficiently. The cause of the migraine—allergies or vision issues or stress—would be the problem. After you create a ticket, you can change the details or add new information to it. Once an incident has been resolved, it can be closed. 25 The following steps are undertaken as part of incident detection and analysis. The objective of an organisation’s incident management process should be to ensure that all those responsible for resolving information security incidents have a firm understanding of three main areas. The ITIL incident management workflow aims to reduce downtime and minimize impact on employee productivity from incidents. He ensures that incidents are handled efficiently and effectively through their life cycle to support INOC clients. Many tools come with their advantages and disadvantages, and one has proven to be a game changer — ServiceNow.
Tier 2and3 service desk:
Wondering what’s the secret to using incident management software. ITIL® 4 defines an incident as. VictorOps has also introduced the “transmogrifier,” a tool that allows everything — from alerts to incident flows — to be customized, making it simple to implement incident management in the way that best suits a given DevOps team. Work better together to resolve issues with cloud based visual outlines and documentation, that help your IT staff track incident response actions through clear process mapping. The incident log called a ticket should include information such as. Powered by automation: Manual and simple tasks can be replaced by automation for a quicker and more efficient ticket resolution process. An effective Incident management system helps facilitate ITIL guidelines, enabling organizations to align their processes with industry standards. As noted above, you can customize the channels customers use to submit requests, but a help center for your JSM instance and portals for each service project are created automatically. Not only will this save you and your team time in the future, but it will also help to reference communication when you need it. On average, companies with an incident response team and a tested incident response plan have an average data breach cost 54.
Does a P2PE validated application also need to be validated against PA DSS?
EG Enterprise is a world leader in converged application and infrastructure monitoring, providing solutions for user experience management, automated diagnosis, and intelligent analytics to solve some of the biggest IT performance challenges of today. This knowledge can then be leveraged to improve processes, mitigate future incidents, and enhance overall operational resilience. The IT Team must also record all the incidents that are not resolved immediately. This document must contain all the details: how to send out the communication, to whom, templates and examples, where to find the distribution lists, etc. Initial categorization and prioritization of Incidents is a critical step for determining how the Incident will be handled and how much time is available for its resolution see checklist Incident Prioritization Guideline. Founded In: 2006Language: Ruby on Rails. Learn how to choose the right tools for effective incident response and seamless operations. Escalation of issues marks the beginning of the incident management lifecycle.
Smartsheet vs Airtable
Unable to open the zip file. Iv In order to facilitate effective implementation of the measures described in subsections 4. Measures how quickly an incident needs to be responded to based on the business needs of the customer. The primary goal is to minimize the impact of incidents and restore services as quickly as possible. Namely, when priority is determined in accordance with the potential impact on users and the business, as well as urgency, it is much easier to understand how quickly the resolution must be achieved and to measure the scope of anticipated damage if the SLA isn’t met. A AI nomenclature and terminology;. This record then becomes the basis for analysis and decisions on managing the incident, including. Which other incidents you’re prioritizing against. Join a community of over 250,000 senior developers. This phase focuses on keeping the incident impact as small as possible and mitigating service disruptions. This is the first step towards resolving the incident.
Incident Management
Information about malicious attempts or suspected incidents and incident history are not shared externally. Can customers opt in to get notifications when I post about an incident. In the last year we have provided responses to over 500 traumatic events affecting people at work. Additionally, many do not work to improve the availability of CTI when in an incident we will give you this knowledge and prep list so you too could benefit from high quality polished CTI in the middle of your Ransomware incident to support IR/IM and even Execs. So, what constitutes a major incident. With the right automation software, also known as ITSM tools, you can program incidents to be flagged automatically. Here are the top four ways implementing ITIL incident management will help you. Closed incidents should only be closed by service desk employees to maintain quality.
Contact Us
What are some important incident management tools. Your canonical record of the incident and its key details live in an incident command center. However, for free software, it’ll do the work just fine. Here is a list of top 12 incident management tools for better monitoring. An incident can be logged through phone calls, emails, SMS, web forms published on the self service portal or via live chat messages. Think: a Wi Fi connection that has gone down or an Android device that has gone on the blink. Mantis BT is flexible, it offers customization features and quickly updates the client through notifications. C Within 365 days of the date of this order, to promote safe, responsible, and rights affirming development and deployment of AI abroad. Instead, the focus of this process is on doing whatever is necessary to restore the service within SLA. Virginia State Police. They provide peer assistance to all emergency service personnel within the Commonwealth before, during or after a critical incident, regardless of race, gender or age. By using an IT service management solution that includes a configuration management database CMDB, for example, you can quickly pinpoint the source of the incident and take action right away. Tools that help augment the Incident Management process should basically provide. Developed by network and systems engineers who know what it takes to manage today’s dynamic IT environments, SolarWinds has a deep connection to the IT community. You should always analyze and learn from incidents to see how you can be better prepared in the future. L2 group is generally a set of people who have the required skills to analyze the issue further. Solarwinds starts at $2,995 including the first year of maintenance and offers a downloadable, free 30 day evaluation. Incident Management interfaces with a number of other ITIL processes. All Incident Management process activities should be implemented completely, operated as applied, measured and amended as necessary. PMP Certification Ultimate Guide – 99. Have regular updates with support teams and the business. Incident Commanders play a crucial role in the successful operation of IT service management ITSM teams. In 1991 the Office of the Fire Commissioner created the Manitoba Critical Incident Stress Management CISM Network as a joint initiative with Manitoba Health. Learn how to use forms to gather more information from your customers and team.